Windows Recall Security Flaws: Why Experts Call the Vault a False Sense of Safety
Do you remember the initial panic surrounding Windows Recall, the AI feature designed to screenshot nearly everything on your PC to create a rewindable activity timeline? Originally slated for Copilot+ AI PCs in June 2024, this controversial tool faced numerous delays due to serious cybersecurity concerns. Although Microsoft has since redesigned the feature and released it to Windows Insiders, security researchers are once again raising the alarm over its safety. Despite these updates, experts argue that the fundamental architecture remains vulnerable to exploitation by malicious actors.
How TotalRecall Reloaded Bypasses Security Measures
Security researcher Alexander Hagenah has developed a new tool called TotalRecall Reloaded that exposes the refreshed Recall's vulnerabilities. The mechanism is deceptively simple: the tool lurks quietly in the background, waiting for the user to access the "locked box" via a Windows Hello prompt. Once the user authenticates and opens the timeline, the tool effectively rides along with the session to extract all captured data.
Hagenah describes this process as snatching the vault's contents like a hydrocolloid bandage on a zit. His research demonstrates that while the security model exists, the trust boundary ends prematurely. TotalRecall Reloaded successfully exploits the moment when decrypted content is sent to an unprotected process for rendering, bypassing the intended isolation.
Key aspects of this vulnerability include:
- The tool remains undetected in the background until the user initiates a Recall session.
- It leverages legitimate Windows Hello authentication to gain temporary access to the secure enclave.
- Once inside, it captures sensitive data such as browsing history, emails, and private messages without triggering additional security blocks.
Microsoft Disputes Vulnerability Claims Despite Critical Risks
Hagenah responsibly disclosed these findings to Microsoft last month, only to be told that his discovery does not constitute a vulnerability. In a statement to The Verge, David Weston, Corporate Vice President of Microsoft Security, claimed the access patterns are consistent with intended protections. He noted that authorization periods have timeouts and anti-hammering protections designed to limit malicious queries.
Microsoft maintains that requiring biometric credentials for every access attempt should restrict latent malware from stealing data during user authentication. However, Hagenah argues that his tool creates precisely the scenario Microsoft's architecture was supposed to prevent. The core issue is not a failure of the encryption or the enclave itself, but rather how the system handles decrypted data outside of those secure boundaries.
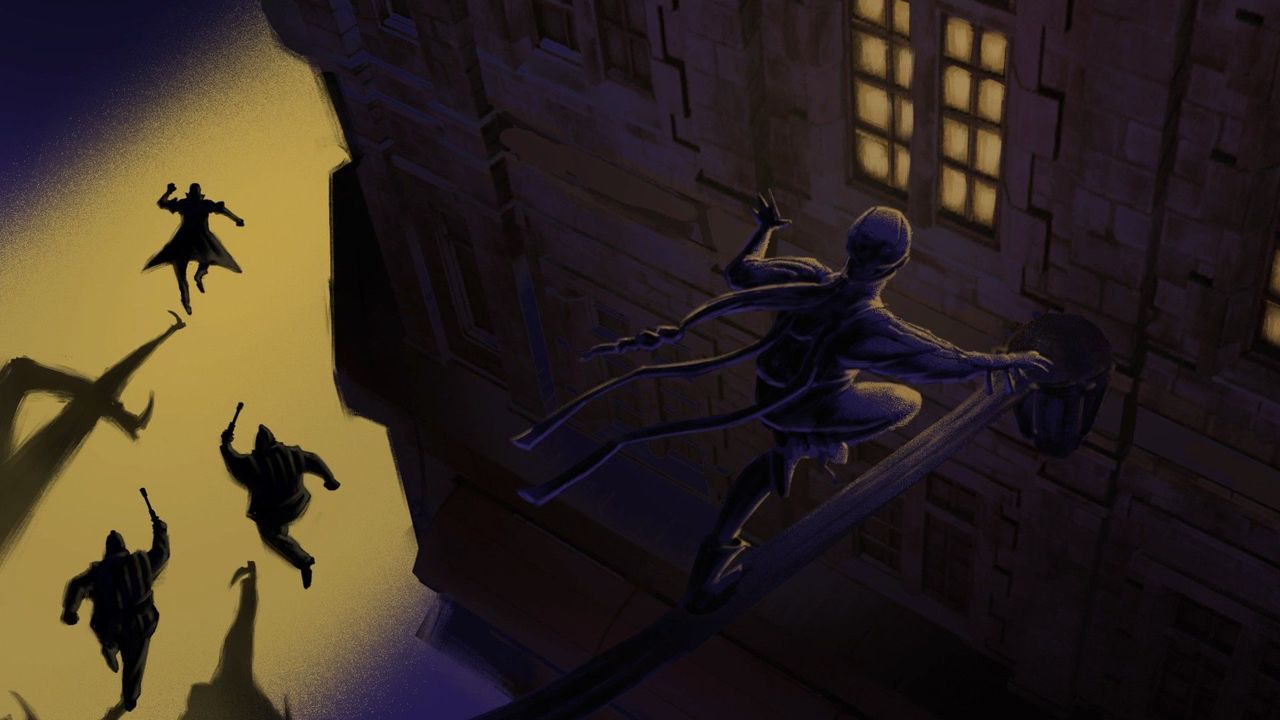
The Titanium Door and Drywall Wall Problem
While Hagenah praised Recall's "rock solid" VBS Enclave, he emphasizes that the cryptographic security is only part of the story. He notes that fixing this issue would likely require a massive overhaul of the OS foundations rather than a simple patch. The fundamental flaw lies in sending decrypted content to an unprotected process for rendering, leaving it exposed during active use.
Hagenah's analogy perfectly encapsulates the current state of Windows Recall security: "The vault door is titanium. The wall next to it is drywall." This means that while the entry point (the authentication) is incredibly strong, the surrounding infrastructure remains weak and susceptible to compromise. As long as the system sends sensitive data to unprotected processes, the risk of data exfiltration persists regardless of how robust the initial lock may be.