Canonical, the organization behind the popular Ubuntu operating system, has confirmed that its services have finally been restored following a massive DDoS attack. The Distributed Denial of Service attack caused significant disruption to critical infrastructure, including websites and software repositories, for five consecutive days.
Recovering from the Ubuntu DDoS Attack
A DDoS attack is designed to paralyze servers and networks by flooding them with an overwhelming volume of requests. These attacks are notoriously difficult to defend against because the malicious traffic often mimics genuine user requests, making it nearly impossible to distinguish between the two without dropping legitimate connections.
Canonical faced this exact challenge over the past week. According to a statement from the company:
"At this much stage, we have implemented mitigations and restored services affected by the Distributed Denial of Service (DDoS) attack."
While the core infrastructure is back online, some users may still encounter latency. Canonical noted that users might experience partially degraded performance on certain services as the company continues its diligent work to resolve any lingering issues.
Impact on Repositories and Security Updates
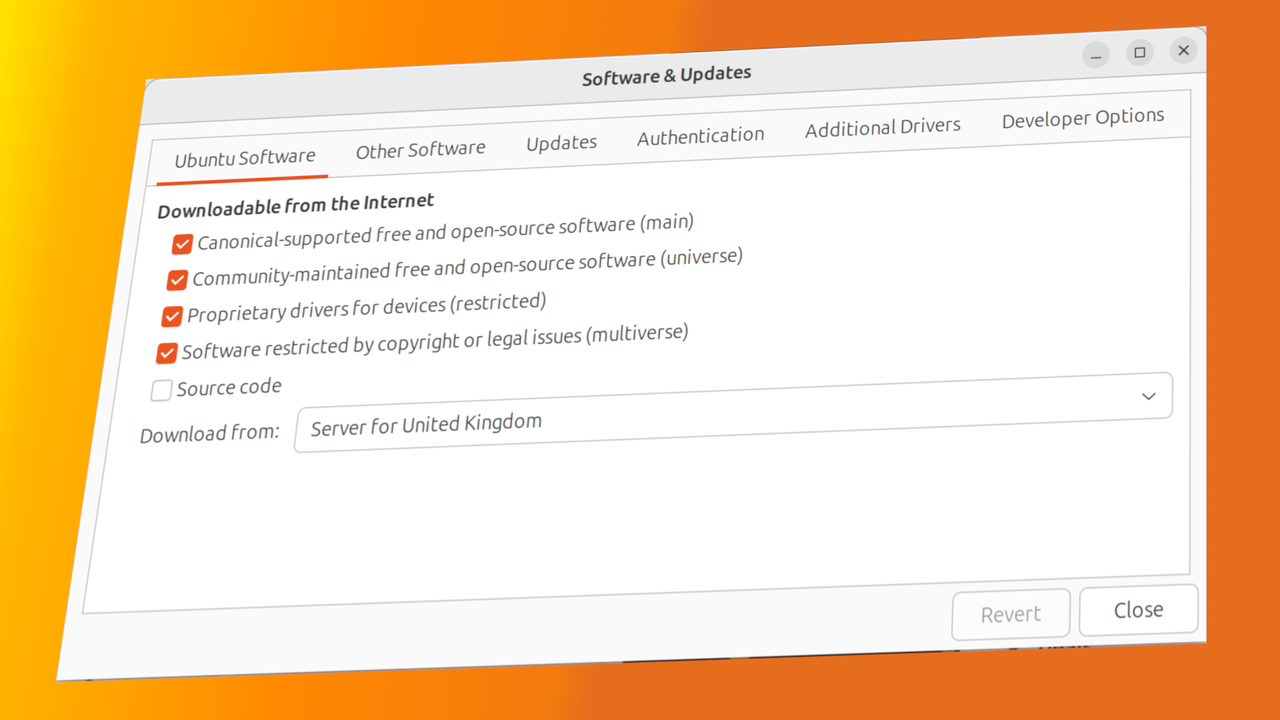
The scale of the disruption was significant. The attack, which first appeared around April 30 or May 1, lasted until Canonical announced a mitigation strategy on May 6. During this window, several key repositories were rendered inaccessible, including those vital for delivering Ubuntu security updates.
This outage placed many administrators in a precarious position, as the lack of access to security patches can leave systems vulnerable. Fortunately, some users were able to mitigate the impact through:
- The use of local mirrors to access essential updates.
- Reliance on specific services that remained intermittently online throughout the attack.
Unclear Motives Behind the Attack
As of now, the motive behind the targeting of Ubuntu remains a mystery. While there has been speculation regarding certain groups—such as "The Islamic Cyber Resistance in Iraq," which reportedly claimed responsibility via Telegram—Canonical has not officially confirmed these claims.
Furthermore, no clear reason has been provided for why such a high-profile open-source operating system was targeted. Given the massive scale of the attack, it remains unclear if this was an act of hacktivism or part of a larger, more complex cyber campaign.