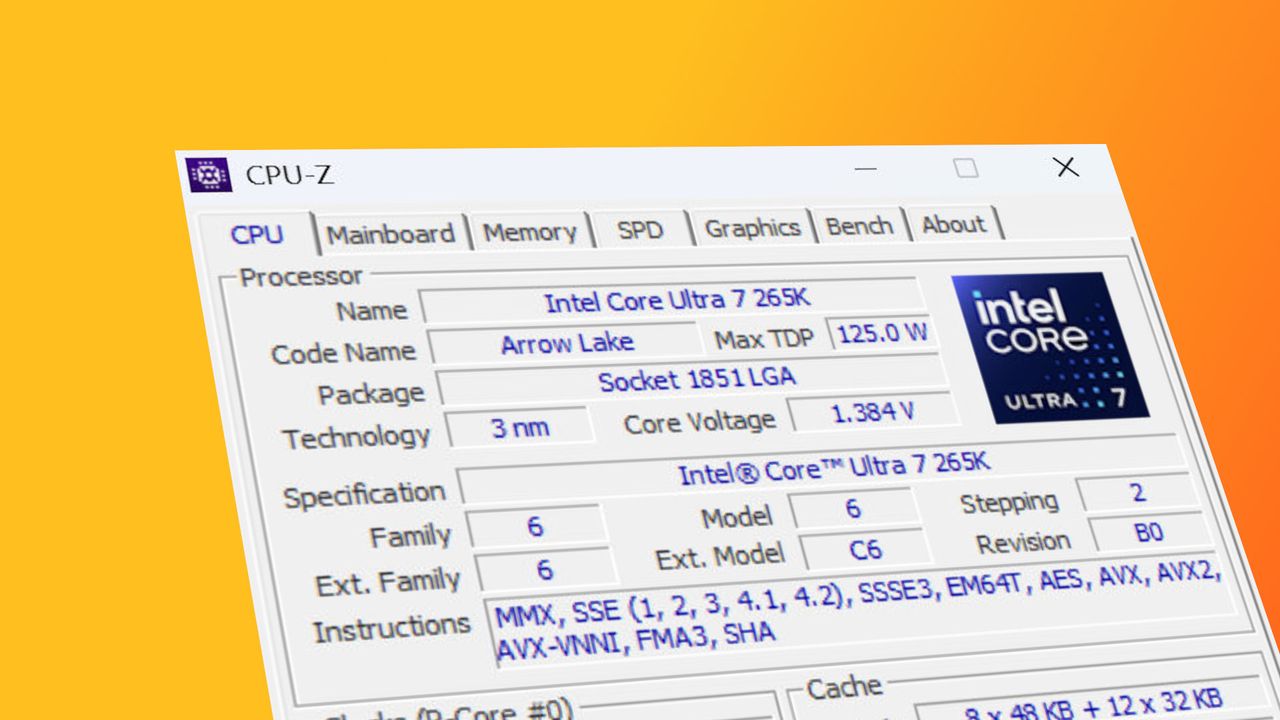
Critical Security Alert: CPUID's Download Page Hacked with Malware-Infested Tools
The gaming PC community was sent into a panic when CPUID, the developer behind beloved utilities like CPU-Z and HWMonitor, saw its official download page compromised. This incident represents a severe breach where the site's popular processor and PC info tools were replaced with links to files containing malware. While the homepage appeared normal, users clicking "download" were directed toward dangerous payloads designed to masquerade as legitimate software.
Sharp-eyed Redditors DMkiIIer and OthoAi5657 were among the first to spot the anomaly just a few hours ago, with their findings swiftly confirmed by security researchers at vx-underground on X. The situation is critical because the malicious files are designed to look authentic, tricking users into executing code that can severely compromise their systems.
How the CPUID Hack Deceived Users and Evaded Detection
The deception employed in this attack was subtle yet highly effective. What looked like standard download links for CPU-Z and HWMonitor actually delivered files with altered names, a Russian setup language, and a completely different wrapper for the installation screen. Instead of downloading hwmonitor_1.63.exe, users were tricked into downloading a file labeled HWiNFO_Monitor_Setup.exe. This deliberate mislabeling caused confusion on social media, leading some to incorrectly believe that the competitor software HWInfo had been compromised, which is absolutely not the case.
Adding to the danger was an immediate warning from anti-virus software upon execution, yet the file masquerading techniques were sophisticated enough to bypass many initial checks. The malware operates almost entirely in-memory and uses proxying of NTDLL functionality from a .NET assembly to evade EDRs and AVs. As noted by Mr. Titus Tech, this is not a run-of-the-mill hijack but a deeply trojanized operation distributing from the compromised domain.
The sophistication of this attack suggests it was executed by a threat group with significant resources. According to vx-underground:
- This malware performs file masquerading to mimic legitimate tools.
- It is multi-staged, meaning it deploys components sequentially to avoid detection.
- It targets the compromised domain (cpuid-dot-com) for distribution.
- The group previously masqueraded FileZilla in early March 2026 and remains active.
Immediate Steps to Protect Your PC from Compromised Downloads
The potential scope of this threat is alarming, as the same group behind the CPUID breach could target other popular PC software tools next. While the identity of the attackers remains uncertain, the pattern of targeting trusted software developers suggests a broader campaign against the gaming and tech community. Users must remain vigilant to ensure their hardware testing and system monitoring activities do not lead to infection.
Your best defense in all of this is to maintain robust security practices immediately:
- Use updated anti-virus/malware packages that are configured for real-time scanning.
- Verify digital signatures by comparing downloaded files from multiple trusted sources to ensure they match official file names, sizes, and hashes.
- Avoid clicking direct download links if the URL or filename looks slightly off, such as variations like HWiNFO_Monitor_Setup.exe.
If you need to verify a tool's integrity for hardware testing, cross-reference the download from the official developer site against a trusted tech publication or community mirror. If files are legitimate, they will be identical in every respect. The update confirms that the issue has been resolved, but the incident serves as a stark reminder of the risks associated with software supply chains.