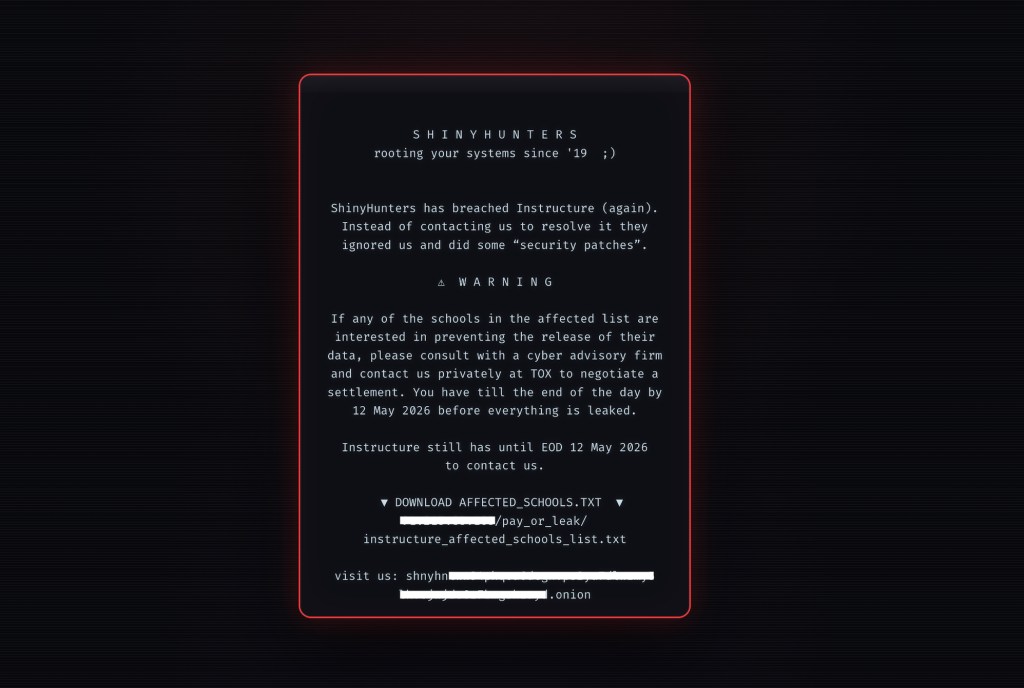
The defaced login page glows with malicious text, demanding attention while students and staff watch helplessly as their credentials are weaponized against them. This stark image underscores the escalating tactics of cybercriminals targeting educational platforms, where trust and privacy are paramount. The recent breach at Instructure—a widely adopted learning management system—has taken a new turn as hackers deface school login pages after claiming responsibility for stealing sensitive data and disrupting access to portals with threatening messages.
Details of the Instructure Breach and Public Threats
A recent disclosure revealed that attackers successfully accessed personal details belonging to thousands of students, including names, emails, and private communications. The situation escalated when the hacking group ShinyHunters announced they had obtained data from nearly 9,000 schools worldwide, potentially affecting over 231 million individuals.
The campaign has moved beyond simple data theft into active disruption:
- Defaced login portals: HTML injections have replaced standard login screens at three specific schools.
- Extortion demands: The defaced pages display ransom-like messages threatening to publish stolen information unless a settlement is reached by May 12.
- Massive scale: The scope of the claim suggests an unprecedented impact on global educational infrastructure.
Tactical Approach: How Hackers Deface School Login Pages
The attackers are employing a combination of social engineering and website manipulation to amplify pressure on Instructure and its users. By utilizing HTML injections, hackers deface school login pages to ensure their demands are impossible for students and faculty to ignore.
The timing of these messages—publicized via leak sites—suggests an orchestrated campaign designed to maximize media coverage and institutional panic. By compromising the front-end login interfaces rather than just backend databases, attackers broaden the immediate impact, disrupting daily operations and potentially exposing active user accounts to further exploitation.
Systemic Vulnerabilities and Industry Implications
This incident raises critical questions regarding authentication infrastructure security within edtech ecosystems. While the exact entry point remains undisclosed, the persistence of the "hack, publicize, extort" pattern indicates that many organizations may still lack robust detection capabilities. The partial outage observed on Instructure’s site during the incident hints at either resource constraints or deliberate disruption attempts designed to complicate remediation efforts.
As edtech adoption accelerates globally, the sector faces increasing demands for stronger security standards and transparent breach notification frameworks. The growing sophistication of ransomware groups, which leverage both technical access and psychological pressure, highlights a significant threat to the resilience of critical educational infrastructure.
Immediate and Long-Term Defensive Measures
For schools currently facing these threats, immediate action is required to mitigate damage. Institutions should focus on the following:
- Stakeholder Notification: Informing all users of potential exposure and recommending immediate credential changes.
- MFA Enforcement: Ensuring multi-factor authentication is deployed across all accessible accounts.
- Vendor Coordination: Working closely with Instructure’s incident response team to confirm system integrity.
In the long term, institutions must reassess third-party risk management. This includes ensuring contractual obligations cover breach scenarios and recovery timelines, as well as implementing proactive measures like regular audits of authentication systems, real-time anomaly monitoring, and comprehensive user education on phishing awareness.