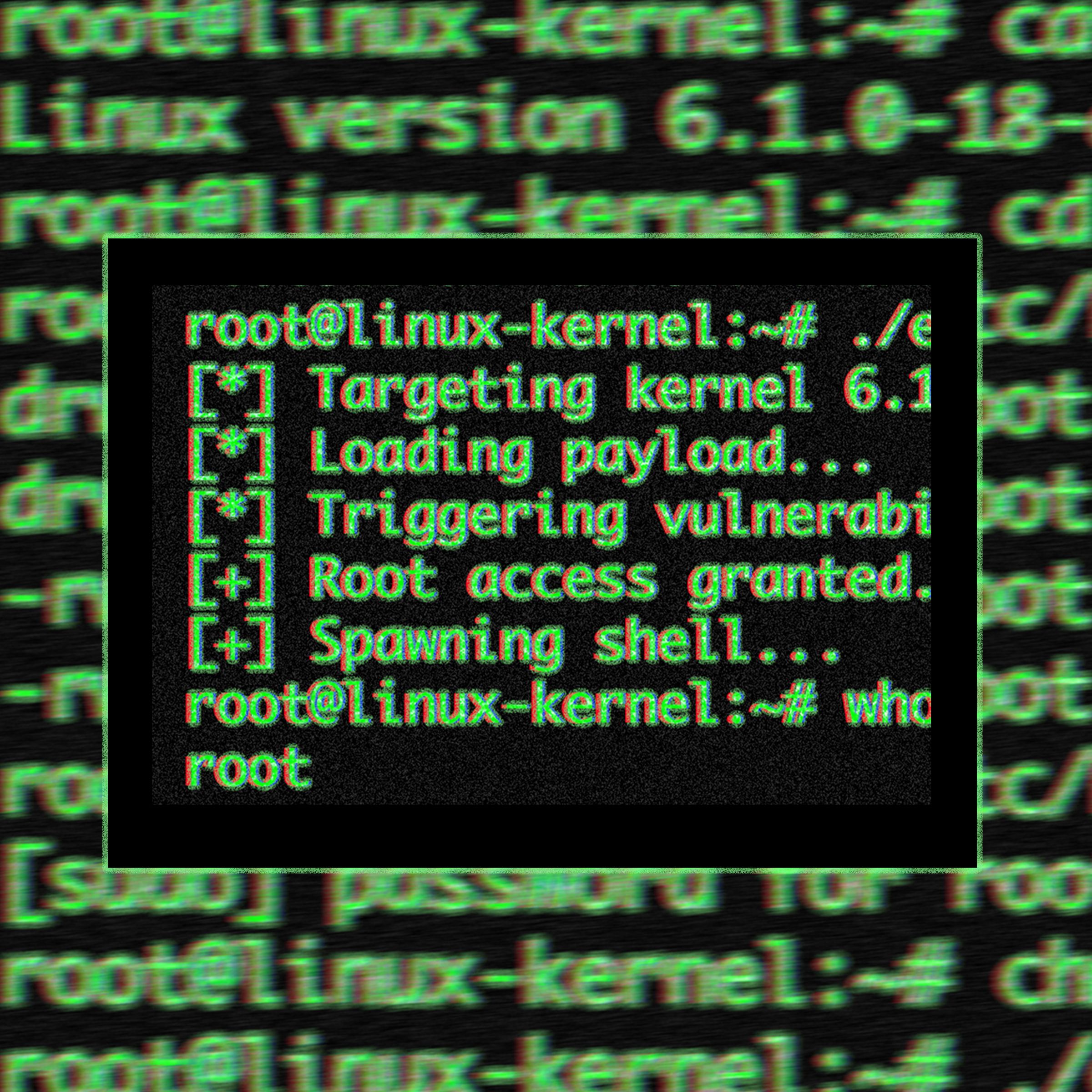
A single script execution on a seemingly isolated container can trigger a cascade of privilege escalations. This dangerous new Linux exploit, known as CopyFail (tracked as CVE-2026-31431), has fundamentally shifted the threat landscape for Linux-based infrastructure. By exploiting a fundamental logic error within the kernel, attackers can bypass the very boundaries that modern cloud computing and containerization rely upon to maintain security.
The Anatomy of a Logic Flaw
Unlike many high-profile kernel vulnerabilities that rely on unpredictable race conditions or complex memory corruption, CopyFail is built upon a "straight-line" logic flaw within the Linux kernel's crypto API. Specifically, the vulnerability resides in how the authenticated encryption (AEAD) template process handles IPsec extended sequence numbers.
During this process, the system fails to properly copy data into its intended destination; instead, it uses the caller's buffer as a scratchpad, inadvertently writing four bytes beyond the legitimate output region. This distinction is critical for potential attackers because CopyFail exploits a predictable logic error, making the reliability of the exploit near-absolute.
The same Python script has been demonstrated to work across vastly different environments—including Ubuntu 22.04, Amazon Linux 2023, and Debian 12—without any modification or tuning for specific kernel versions. Once an attacker gains even the most minimal, unprivileged access to a system, they can execute this script to promote themselves to root status.
Breaking Container Boundaries with this Dangerous New Linux Exploit
The true danger of CVE-2026-31431 lies in its ability to collapse the logical isolation provided by modern orchestration frameworks. In a world where multi-tenant architecture is the standard, the kernel acts as the final arbiter of truth and separation. When that arbiter is compromised, every resident on that host becomes vulnerable.
The blast radius of this exploit extends far beyond individual workstations:
- Kubernetes Clusters: An attacker occupying a single container can break out of its sandbox to gain control over the entire node.
- CI/CD Pipelines: Malicious pull requests containing exploit code could be automatically executed by automated testing environments.
- Windows Subsystem for Linux (WSL2): Users running Linux environments on Windows are also at risk of privilege escalation.
- Shared Hosting and Cloud Infrastructure: A single compromised tenant can lead to the compromise of every other client sharing the underlying kernel.
As researchers from Theori have noted, the vulnerability doesn't necessarily provide the initial entry point; rather, it radically changes the landscape in the seconds following an initial breach. This "local" privilege escalation (LPE) effectively turns a minor breach into a platform-wide catastrophe.
The Crisis of the Patch Gap
The emergence of CopyFail has also sparked a heated debate regarding the ethics of vulnerability disclosure and the efficiency of the Linux ecosystem's response. While the Linux kernel security team has released patches for several versions—including 6.19.10, 6.12.85, and 5.15.204—a significant "patch gap" remains.
Critics have pointed out that many major Linux distributors are slow to incorporate these upstream fixes into their stable releases. This creates a window where this dangerous new Linux exploit is effectively a zero-day for much of the world's active infrastructure. While some distributions like Arch Linux and RedHat Fedora have moved toward remediation, others remain in a state of high exposure.
The industry now faces intense scrutiny regarding how researchers coordinate with vendors before going public. For administrators, the directive is clear: immediate investigation into kernel versions and the rapid application of all pending updates is the only way to close this window of opportunity for attackers.