Instructure and the Unprecedented Hackers’ Deal
In the high-stakes world of cybersecurity, the standard response to a data breach is swift denial and legal countermeasures. However, Instructure, the prominent edtech provider behind the widely used Canvas learning platform, has chosen a radically different path. The company has struck a deal with the hackers who breached its systems, marking a rare and controversial pivot in crisis management.
This agreement comes after Instructure suffered two significant security incidents, forcing the company to negotiate directly with the criminal groups responsible. While traditional protocols dictate that organizations reject ransom demands outright to avoid encouraging further crime, Instructure’s approach blurs these ethical lines. The decision raises critical questions about how educational technology providers protect sensitive data when faced with sophisticated, persistent threats.
The Dual Breach: A Crisis of Scale and Visibility
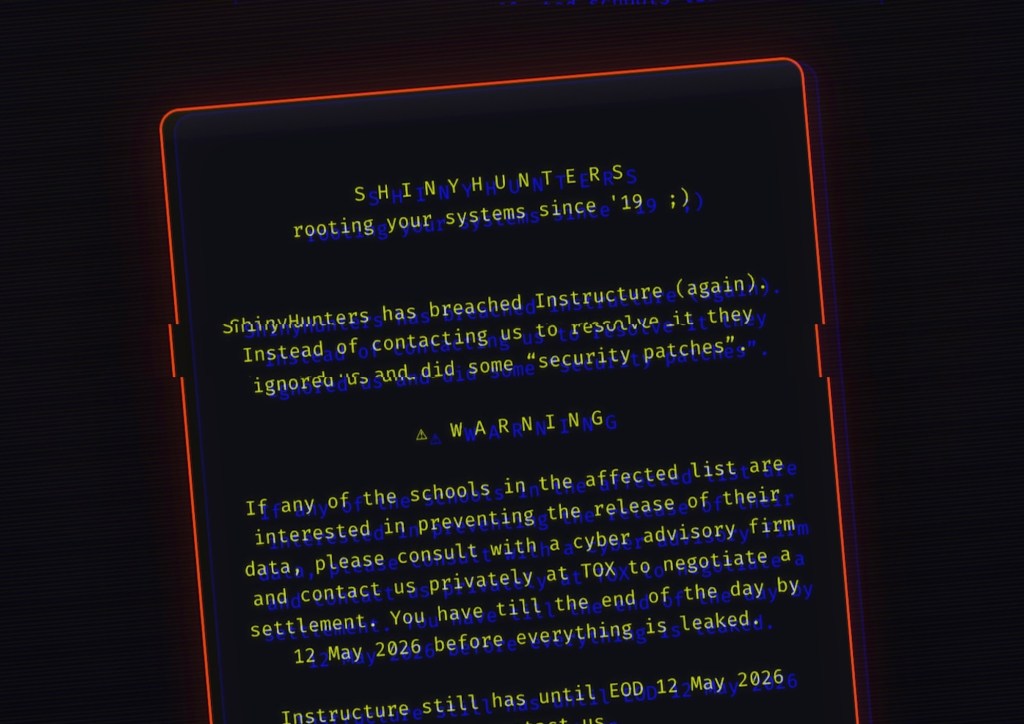
The catalyst for this unusual arrangement was a sequence of two distinct but related cyberattacks that exposed the vulnerabilities in Instructure’s infrastructure. The first incident occurred in April, when the hacker group known as ShinyHunters infiltrated the company’s systems.
This initial breach was severe in scope. ShinyHunters successfully exfiltrated sensitive data from nearly 9,000 schools relying on Instructure’s platform. The stolen troves included:
- Student and staff identities: Names and personal email addresses were compromised.
- Private communications: Internal messages and documents were accessed.
- Institutional data: Information potentially weaponized against thousands of schools.
Weeks later, the situation escalated with a second breach. This time, the attackers defaced Canvas login pages. This tactic served as a form of psychological warfare, amplifying pressure on Instructure through public shaming and service disruption. The defacement signaled to the public that the company was under active siege, increasing the urgency for a resolution.
A Shift in Cybersecurity Norms
Instructure’s decision to engage with the hackers marks a critical shift in how organizations handle extortion. According to reports, the company secured a specific condition for halting the threat: confirmation that the stolen data had been destroyed. This assurance eliminated the immediate risk of the data being leaked or sold on the dark web.
While financial terms remain undisclosed, the core of the agreement focused on cessation of hostilities rather than simple payment. Instructure pledged no further engagement with the criminal actors, effectively buying peace rather than fighting a prolonged battle. This contrasts sharply with official guidance; the FBI and other government advisories consistently discourage ransom payments, citing that compliance encourages further criminal activity.
Key aspects of the agreement include:
- Data Destruction Assurance: The primary condition for stopping the threat was verified deletion of stolen files.
- Silent Resolution: Rumors suggest funds may have changed hands, though Instructure has not confirmed direct payments.
- Regulatory Tension: The deal operates in tension with federal warnings against complying with cybercriminals.
Lessons for the EdTech Sector
This incident highlights systemic weaknesses in legacy security frameworks, particularly those underpinning education. With ShinyHunters threatening to leak data unless demands were met, institutions faced a delicate balance between protecting privacy and avoiding escalation.
The involvement of the FBI signals heightened scrutiny of such incidents, urging stakeholders to prioritize proactive defense over reactive measures. The case serves as a cautionary tale for the broader edtech industry, demonstrating that outdated security infrastructure leaves schools exposed to sophisticated attacks.
Transparency and collective action are now imperative. Clear communication with affected parties is critical, even amid uncertainty, while collaboration between companies, regulators, and educators remains essential for resilience. As digital platforms become central to daily operations, organizations must invest in robust safeguards and prepare nuanced response strategies.
Instructure’s deal proves that sometimes, the most unconventional solutions are necessary to mitigate unprecedented threats. The balance between ethical principles and pragmatic survival will define how the sector navigates an ever-evolving threat landscape.