The Physical Scale of Global Malware
The global threat landscape has reached a new milestone: the two largest repositories of known malware samples now collectively hold enough data to fill an entire warehouse floor. Malware research groups and commercial platforms have effectively evolved into massive data centers, storing terabytes and even petabytes of malicious code. These archives are far from static libraries; they serve as active resources essential for training detection models, reverse-engineering new attack techniques, and informing policy decisions across governments and private sector firms.
This sheer volume reflects both the breadth of cybercrime and the competitive race among threat actors to outpace defensive measures. To truly grasp the magnitude of this digital hoarding, we must look at the data through a physical reality lens.
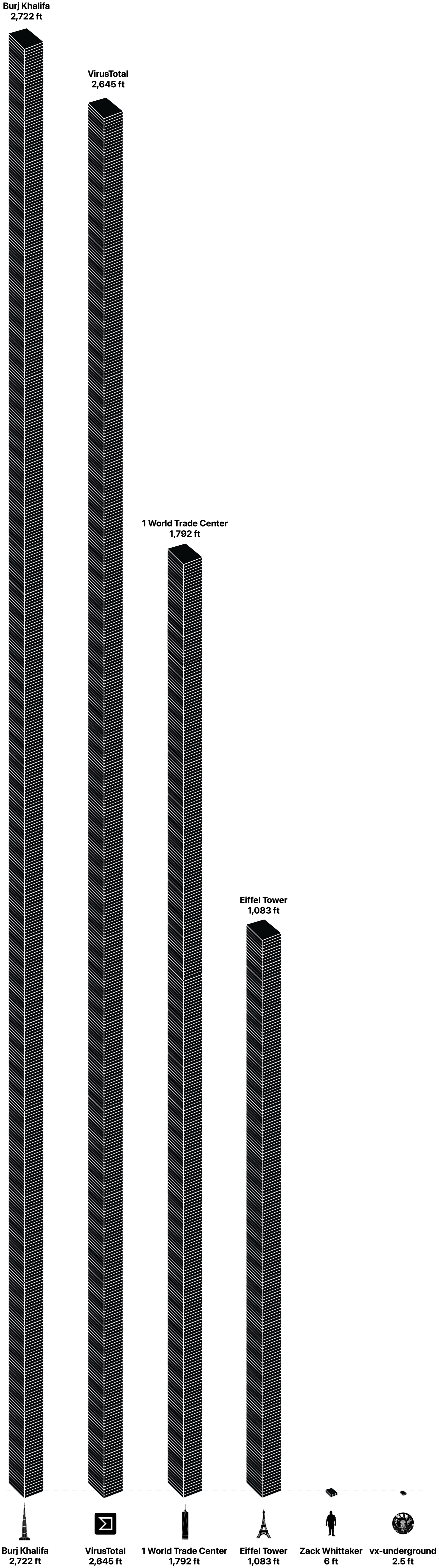
From Data to Physical Height
To visualize this scale, consider that a standard 1TB internal hard drive stands roughly one inch tall when stacked vertically. Assuming identical form factors and ignoring real-world inefficiencies like gaps between platters or casing thickness, we can convert raw capacity into height using simple geometry.
The resulting stacks reveal staggering proportions:
- 30 Terabytes (vx-underground): This archive requires a stack approximately 30 inches high, or about 2.5 feet.
- 31 Petabytes (VirusTotal): This massive repository demands a stack of 31,744 drives, reaching roughly 2,645 feet.
For context, an average human stands six feet tall. The VirusTotal archive alone would tower nearly half a mile if laid end to end or stacked above a typical office building.
Visualizing the Impact
Stacking these drives vertically creates a structure that dwarfs many urban landmarks. The Burj Khalifa, currently the tallest building in the world, rises just over 2,700 feet. This means VirusTotal’s data could theoretically reach slightly higher than the world's tallest structure if condensed into a single column.
However, such stacks remain purely theoretical. Practical storage solutions prioritize density and redundancy rather than vertical display, hiding this immense capacity within dense server racks that consume significant power and cooling resources.
Implications for Security and Research
This physical metaphor underscores why cyber threat intelligence is treated like critical infrastructure. Each terabyte represents countless potential attack vectors, while petabyte-scale collections enable machine learning models to spot subtle patterns invisible to human analysts.
However, maintaining such resources requires significant investment in hardware, cooling, and network bandwidth. This creates natural barriers that also concentrate control among a few major players. As attackers continue to innovate, defenders must match them with equally robust data practices, ensuring both breadth of coverage and depth of insight. The journey from code to physical stack illustrates not just size, but the strategic importance of information in modern conflict.