Congressional Inquiry Demands Transparency from Instructure Following Canvas Data Breaches
The intersection of education and technology has become a primary target for cybercriminals, and the recent scrutiny of Instructure highlights the severe risks inherent in digital learning platforms. With over 10 million student records compromised across global education networks, the U.S. House Homeland Security Committee has issued a formal demand for answers from the company behind the widely used Canvas learning management system.
This legislative action, spearheaded by Committee Chair Representative Andrew Garbarino, signals a decisive shift in how lawmakers view the cybersecurity obligations of educational technology providers. The gravity of these incidents exposes the fragility of modern digital dependencies, forcing a reckoning with how vast amounts of sensitive student data are protected.
Key Areas Under Legislative Scrutiny
The Committee’s investigation is not merely a formality; it seeks to dissect the specific failures that allowed hackers to repeatedly breach Instructure’s systems. Lawmakers are demanding clarity on several critical fronts:
- Incident Response Efficacy: Officials require a detailed timeline of each attack to understand how long the breaches persisted before detection.
- Data Handling Protocols: The inquiry focuses on the specific types of stolen information, including personally identifiable information (PII) and private academic records.
- Coordination with Federal Agencies: Investigators are examining the extent of Instructure’s collaboration with the Cybersecurity and Infrastructure Security Agency (CISA) during and after the incidents.
- Ransom Payments: A critical point of contention is whether Instructure paid the attackers, a practice that security experts warn incentivizes future extortion attempts.
The Role of ShinyHunters and Cybersecurity Failures
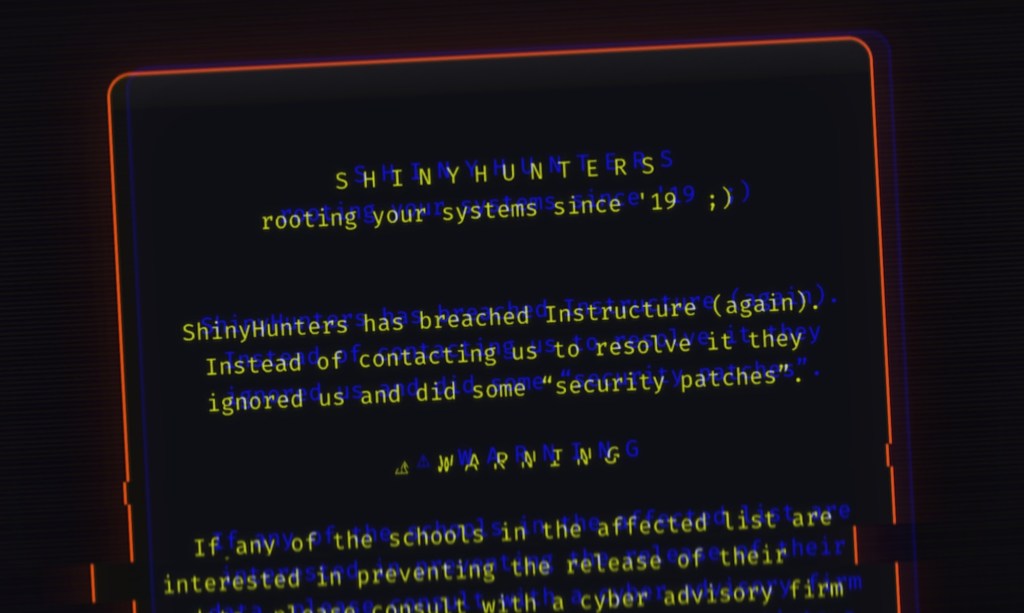
Instructure has faced intense criticism for its handling of two high-profile breaches that resulted in not only data theft but also visible website defacements. A ransomware group known as ShinyHunters claimed responsibility for both incidents, asserting that they would delete the stolen data upon receipt of payment.
While the exact amount paid remains undisclosed, the fact that payments were made underscores a troubling cycle of vulnerability in the edtech sector. Security experts argue that such practices do not resolve the underlying security gaps but rather perpetuate them, encouraging further attacks on other institutions that may lack the resources or resolve to fight back.
Broader Implications for EdTech Regulation
The Committee’s investigation reflects a growing legislative focus on the obligations of vendors who safeguard educational data. As digital transformation accelerates in classrooms nationwide, regulatory scrutiny is poised to intensify significantly. Companies like Instructure now confront heightened expectations for:
- Transparency: Clear and timely communication regarding breaches.
- Proactive Threat Mitigation: Advanced security frameworks that prevent unauthorized access.
- Accountability: Concrete measures to ensure lessons are learned from past incidents.
This case sets a potential precedent for how lawmakers will balance technological innovation with user protection. The outcome may reshape industry standards, compelling edtech firms to prioritize robust security frameworks amid escalating cyber threats.
Conclusion
The U.S. legislative push against Instructure reflects a maturing approach to digital governance, emphasizing that technology in education must meet stringent safety benchmarks. For now, the spotlight remains on how swiftly companies can adapt to evolving threats while upholding trust among users—a challenge that grows more pressing with each new breach.
The ripple effects of this investigation extend beyond compliance, potentially influencing funding allocations for edtech research and shaping public perception of digital learning tools. As discussions continue, the emphasis on proactive defense mechanisms and ethical data stewardship will likely dominate future policy debates, defining the resilience of the educational landscape in the years to come.