The era of simple password protection is rapidly coming to an end as digital credentials evolve from mere access points into gateways for highly sensitive, personalized data. As artificial intelligence moves from an experimental novelty into a core component of professional workflows, the potential damage of an account takeover has scaled exponentially. To combat this growing threat, OpenAI is introducing OpenAI Advanced Account Security to protect its most vulnerable users.
Eliminating the Human Element in Authentication
The rollout represents a significant shift toward a zero-trust architecture. By introducing this optional tier, OpenAI is attempting to close the loop on one of the most common attack vectors: social engineering. In traditional setups, an attacker might compromise a user's email or trick a support representative into resetting a password.
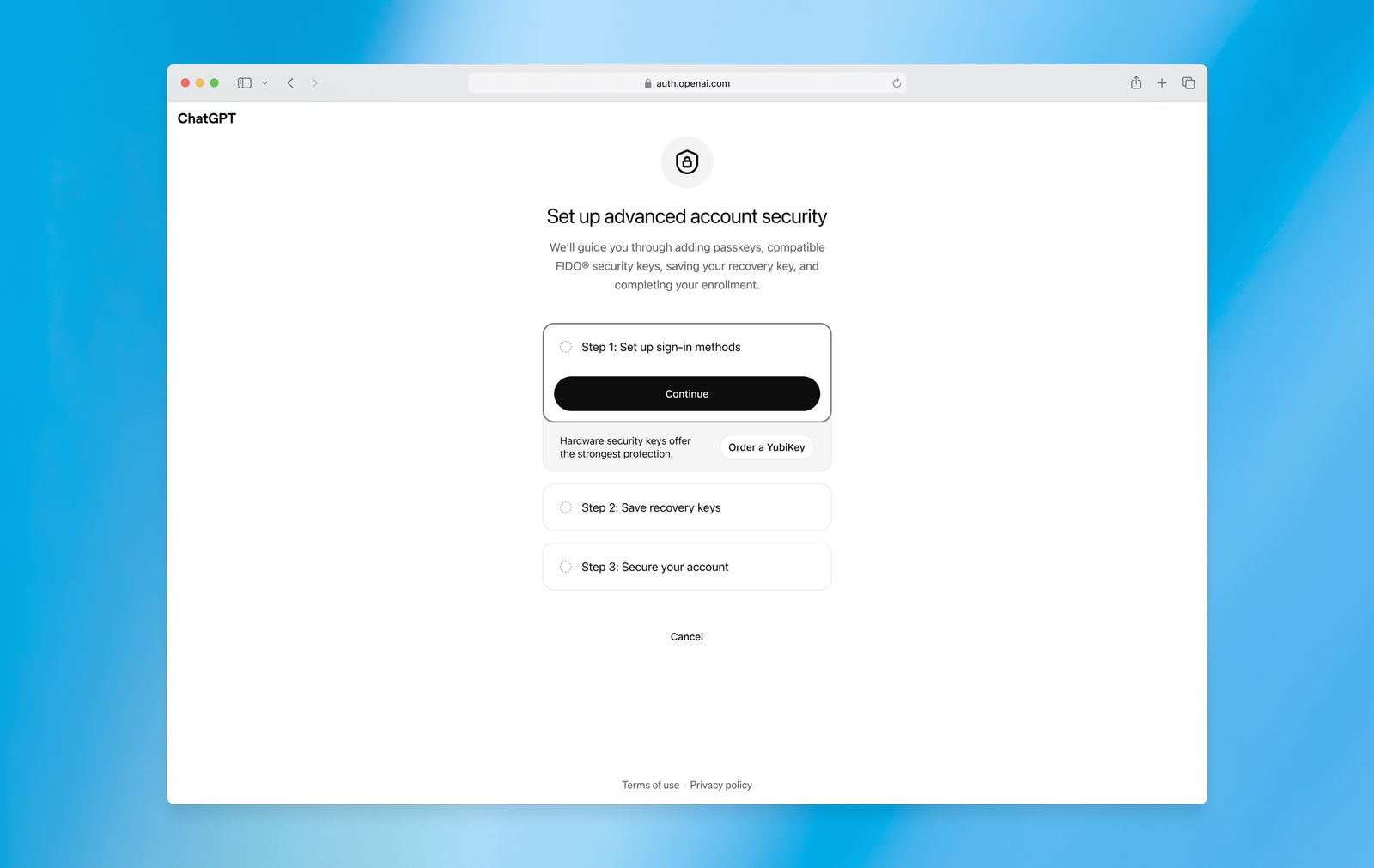
OpenAI is effectively removing the human element from this vulnerability chain by ensuring that even their own support staff cannot facilitate account recovery. Under this new protocol, users can no longer rely on traditional passwords. Instead, the system mandates the use of two physical security keys or passkeys to verify identity.
This move mirrors long-standing high-security protocols established by companies like Google, which has offered similar advanced protection tiers for nearly a decade. By forcing authentication through hardware, OpenAI is making successful phishing attacks—which rely on tricking users into entering credentials on fraudulent sites—mathematically much more difficult.
The technical implications are profound for the recovery process itself. The feature entirely eliminates email and SMS-based recovery routes, which are notorious for being intercepted via SIM swapping or inbox compromise. To assist with this transition, OpenAI has partnered with Yubico to provide more affordable YubiKey bundles, acknowledging that the cost of hardware is often a barrier to entry.
Core Features of OpenAI Advanced Account Security
The deployment of these features is specifically targeted at users whose professional lives depend on the privacy of their AI interactions. For journalists, political dissidents, and researchers, a compromised ChatGPT account is not just a loss of access; it is a potential leak of sensitive intelligence or confidential communications.
The OpenAI Advanced Account Security tier introduces several automated safeguards to ensure that even if a device is temporarily accessed, the footprint of the intrusion is minimized:
- Mandatory phishing-resistant authentication via hardware keys or passkeys.
- Automatic exclusion from model training, ensuring conversations are not used for future iterations by default.
- Reduced session windows, requiring more frequent re-authentication on active devices.
- Real-time login alerts that notify users of any new active sessions appearing on the dashboard.
By making training exclusion the default setting for these accounts, OpenAI is addressing a growing concern regarding data sovereignty. As AI models become more integrated into corporate and governmental workflows, the distinction between "convenience" and "security" is becoming increasingly blurred.
The Path Toward Mandatory Compliance
The transition period for these security measures is already beginning with a clear mandate for specialized users. Starting June 1, members of OpenAI’s Trusted Access for Cyber program—a group comprised of cybersecurity professionals and researchers—will be required to enable this advanced security mode.
Unless these users can provide an alternative attestation of phishing-resistant authentication through enterprise single sign-on (SSO) mechanisms, their access will be restricted by these stricter protocols.
This move signals a broader industry trend where the "opt-in" nature of high-level security is being replaced by mandatory compliance for critical infrastructure. As AI becomes an increasingly centralized tool for global industry, defending against sophisticated state-sponsored actors will depend entirely on these hardware-rooted authentication methods. The era of trusting a string of characters is over; the future of digital identity lies in the physical possession of cryptographic keys.